Sales Inquiries: (855) 525-3885
Existing Clients: (818) 249-1962
Your EXPERT, EMPLOYEE-OWNED IT SUPPORT Department
Why Businesses Work with GenCare
111% Satisfaction Guarantee
We stand behind our IT services with a 111% money-back guarantee, ensuring zero financial risk.
Employee-Owned, Client-Focused
Our dedicated IT team prioritizes long-term partnerships, delivering personalized IT services tailored to your needs.
Seamless, No-Overlap Transitions
Switching IT providers is hassle-free with our structured process, ensuring no overlap in MSP billing.
Committed to Strong Partnerships
We build lasting relationships through reliable IT services, ensuring your business always has a trusted technology partner.
Are You Struggling With IT Services That Don’t Prioritize Your Business Needs?
If You're Fed Up with IT (and IT Companies),
We Understand Why
Technology should support your success, not slow you down. If constant IT issues, unresponsive support, or outdated systems are holding you back, it’s time for a change. You need an IT partner that understands your business and delivers proactive solutions.

Jeff Baker
Vice President

Why Settle for IT Services That Ignore Your Challenges and Leave You Frustrated?
Your business deserves IT services that prioritize partnership, responsiveness, and long-term success. If you're tired of waiting for support, dealing with unexpected downtime, or struggling with unreliable providers, GenCare offers a seamless, risk-free transition backed by our 111% satisfaction guarantee and a team committed to your success.
Take control of your IT with a trusted partner who guarantees results. Schedule a 30-minute call today and discover how our no-risk IT services can transform your business.
Satisfied Customers
Schedule an Appointment Today
Client Success Stories
What We Do
Managed IT Services
Gain reliable, proactive IT support that keeps your business running smoothly and efficiently.
Cybersecurity Solutions
Protect your business with advanced security solutions that defend against evolving cyber threats and risks.
Disaster Recovery Planning
Ensure business continuity with recovery strategies that minimize downtime and protect critical data.
VoIP Phone Systems
Improve communication with scalable VoIP solutions offering clear calls and seamless business tool integration.
Azure Cloud Solutions
Enhance flexibility and security with Azure cloud services designed for performance and scalability.
Microsoft 365 Support
Boost productivity with expert Microsoft 365 support, ensuring seamless integration and collaboration.
What Clients Say About Us
The More You Know...
Stay informed with expert insights on IT services, cybersecurity, cloud solutions, and business technology trends. Our blog helps you navigate challenges, optimize efficiency, and strengthen your IT partnership with proactive strategies and real-world solutions.

Heatwave Tech Tips: Preventing Overheating and Extending Device Lifespan
Summer sunshine is great for beach days and barbecues. But it’s not so great for your tech. Whether you’re working from a sunny patio or traveling with your devices, rising temperatures can quietly ta... ...more
IT Services ,Cybersecurity
July 11, 2025•4 min read

How AI Is Supercharging Cyber Threats This Summer
Long days and warm nights make summer the perfect time to unplug and unwind. But while you’re kicking back, cybercriminals are ramping up. And this year, they’ve got a powerful sidekick: artificial in... ...more
Cybersecurity
July 07, 2025•4 min read

Cyber Insurance Won’t Save You from Yourself (But Here’s What It Will Do)
Let’s have a real talk about cybersecurity insurance. Because there’s a whole lot of "I thought I was covered..." happening out there, and it’s costing small businesses big time. You think it’s boring... ...more
IT Services ,Cybersecurity &IT Consulting
June 13, 2025•3 min read
Frequently Asked Questions
How do we get support?
By email or phone
How quickly do you respond?
15 minutes
Oh yeah, can you prove it?
Are you serious about getting fast support and resolving your issues faster than your current MSP? We can work with you. Our busiest deadline-driven customers are the ones that stick with us the longest. 1/3rd of our reviews on Clutch highlight fast response as their #1 reason for choosing GenCare. The other 2/3rds talk about the things we achieve once we’ve shown up.
Will you come onsite?
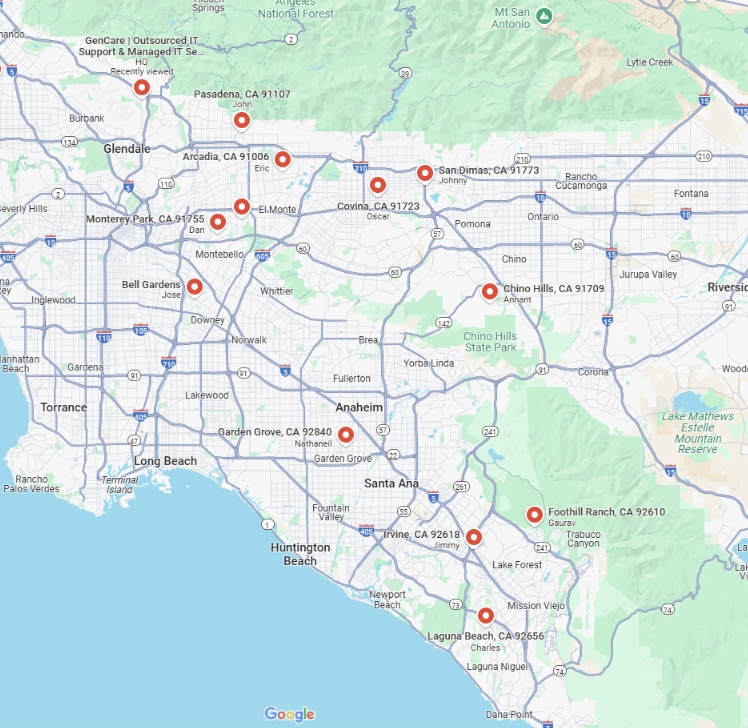
Yes. 7.1% of our support tickets were closed onsite last year. Every contract includes onsite support in LA.
What’s off the table completely?
Thanks to our insurance company, we won’t work on ladders, in attics, or move your furniture.
Experience IT Services Built on Partnership and Trust
GenCare is more than an IT provider—we're your dedicated partner, committed to your success. With our employee-owned team, proactive support, and 111% satisfaction guarantee, your business receives IT services designed for long-term stability and growth.
Call (855) 525-3885 today or fill out the form below to schedule your appointment and experience a real partnership in IT.