Sales Inquiries: (855) 634-5557
Existing Clients: (818) 249-1962
The Truth About Shadow IT
Not every cyber risk comes from the outside. Some walk right in the front door ... in the form of tools, apps, and devices your own employees are using without asking. It’s called shadow IT. And it’s ... ...more
Protect Your Business
January 06, 2026•3 min read

These Cyber Threats Are About to Get a Whole Lot Worse
Cybersecurity threats don’t stand still. They adapt. They get smarter. And every time technology takes a step forward, attackers figure out how to twist it to their advantage. ...more
Protect Your Business
December 02, 2025•3 min read

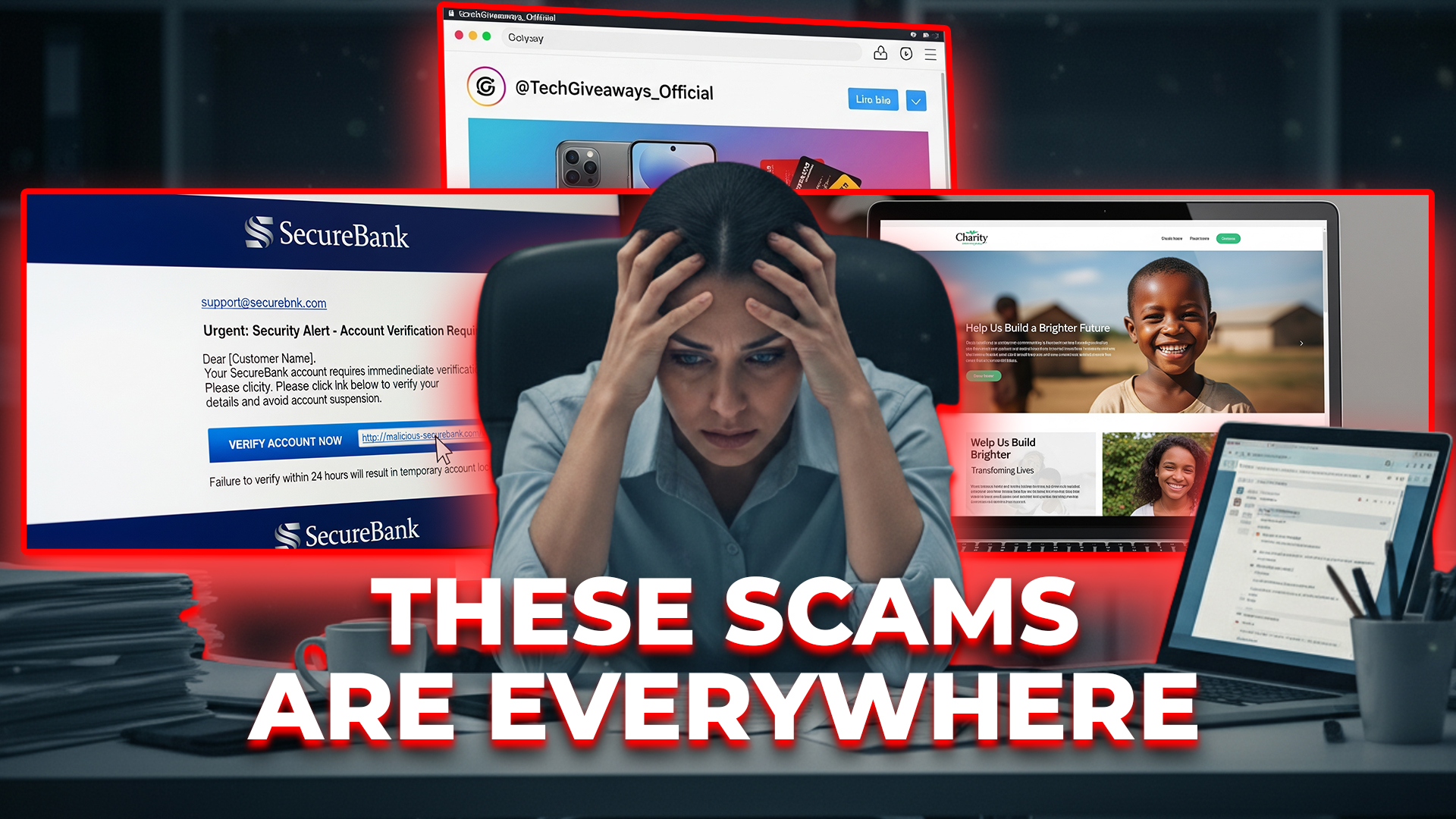
These Scams Are Everywhere (And They Work)
Cybercriminals don’t take days off ... and they don’t wait for a “good” time to strike. They prey on moments when people are busy, distracted, or rushing. ...more
Protect Your Business
November 04, 2025•3 min read
YOU Are The Hacker’s Shortcut In
Hackers don’t need to break into your systems.. they can talk their way in. Here’s how social engineering works, the tricks cybercriminals use, and the steps we take to stop them. ...more
Protect Your Business
October 14, 2025•3 min read

The Costliest Cyber Fails in History
Cyber disasters often start small, like a missed update, a click, or a tiny mistake. The difference between a close call and a catastrophe is proactive protection. Here’s how we prevent real-world cyb... ...more
Protect Your Business
October 10, 2025•3 min read

The Silent IT Budget Killer
Most business owners treat their IT budget like a gym membership in January ... they sign up, pay every month, and never check if they’re actually getting results. That’s why so many companies waste t... ...more
Protect Your Business
September 19, 2025•3 min read

Want To See How Simple IT Can Be?
Schedule a 15-minute call to tell us about your business.
Find out if we're the right fit for you.
Decide if you want to work with us.


